Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
[ad_1]
Coordinated vulnerability disclosure (CVD) begins when not less than one particular person turns into conscious of a vulnerability. It might’t proceed, nevertheless, with out the cooperation of many. Software program provide chains, software program libraries, and part vulnerabilities have developed in complexity and have change into as a lot part of the CVD course of as vulnerabilities in distributors’ proprietary code. Many CVD instances now require coordination throughout a number of distributors. This submit, which relies on a not too long ago revealed particular report, introduces Vultron, a protocol for multi-party coordinated vulnerability disclosure (MPCVD).
Since releasing our first advisory in 1988, CERT/CC has sought to enhance the professionalization of the world’s CVD practices. Drawing on work throughout the many years, our method has been to distill and formalize what we find out about this course of. This work grew out of quite a few advert hoc particular person efforts to coach software program distributors and the safety analysis neighborhood as they engaged our providers in coordinating, analyzing, and publishing vulnerability reviews, together with the next:
Along with our personal efforts, now we have additionally participated in (and at instances led) the event of associated ISO/IEC requirements round vulnerability disclosure, together with
In September 2022, we launched Vultron, a proposed protocol for MPCVD. The total report, Designing Vultron: A Protocol for Multi-Social gathering Coordinated Vulnerability Disclosure (MPCVD), describes a high-level protocol that we consider gives a basis for course of interoperability amongst CVD stakeholders and factors the way in which towards technical implementation in instruments like VINCE and different CVD service platforms.
Whereas I’ve led efforts to develop the Vultron protocol, it represents solely a bit of a broader effort to enhance CVD practices. The report wouldn’t have been potential with out ongoing dialogue with my CERT Division colleagues together with Eric Hatleback, Artwork Manion, Brad Runyon, Vijay Sarvepalli, Sam Perl, Jonathan Spring, Laurie Tyzenhaus, and Chuck Yarbrough.
The Vultron protocol begins with semantic interoperability as a result of CVD contributors have to first agree on what they imply once they speak about their processes. No quantity of syntactic interoperability (e.g., knowledge trade format specs or APIs) may help if the interpretation of that knowledge differs for the sender and the receiver. The Vultron protocol is designed to deal with each CVD and MPCVD instances. Actually, the protocol doesn’t discriminate between them; it merely treats “regular” CVD as a particular case of MPCVD through which the variety of distributors is 1.
Particularly, the Vultron protocol is constructed round three distinct however interacting processes, which we describe within the report as deterministic finite automata (DFAs):
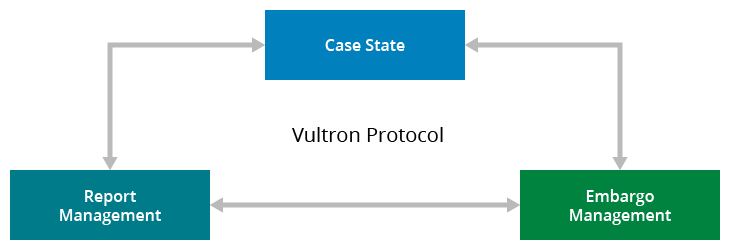
Determine 1: Three processes (case state, embargo administration, and report administration) work together to kind the Vultron Protocol.
The Vultron protocol encompasses each native and international points of the CVD course of. For instance, whereas the report administration course of is native to a selected case participant, the embargo administration course of is anticipated to be shared throughout all case contributors. Equally, parts of the case state mannequin are international to the case, whereas others are particular to particular person contributors. Our intent, nevertheless, is to depart loads of room for stakeholders to implement their very own inside processes to go well with their particular person wants. Our purpose with the Vultron protocol is to supply a set of related abstractions to map numerous organizations’ inside processes onto a generalized workflow that promotes coordination of effort and improves the communication of case standing throughout stakeholders.
Our report on Vultron consists of detailed commentary on how the Vultron protocol may be applied and descriptions future work. Appendices are supplied that map the Vultron protocol onto current work together with SSVC v2, ISO/IEC 30111:2019, ISO/IEC 29147:2018, and ISO/IEC TR 5895:2022 (Cybersecurity—Multi-party coordinated vulnerability disclosure and dealing with).
And sure, followers of a sure colourful anime large mecha composed of 5 discrete robots with human pilots may observe greater than a passing metaphor in the concept it takes a cooperative and coordinated effort for a fancy human/machine partnership to attain some defensive objectives.
Though now we have completed some inside proof-of-concept growth to discover points of the Vultron protocol, it has not been absolutely applied but. Nor have we accomplished our evaluation of its properties. As a result of measurement and scope of what we predict it would change into, nevertheless, we needed to share it now as a proposal so we will start growing a neighborhood of curiosity amongst related stakeholders, together with, however not restricted to
When you can count on to listen to extra from us concerning the Vultron protocol sooner or later, we’re serious about your suggestions on the protocol now we have proposed within the report. Some questions to contemplate in your suggestions embody the next:
Additionally, as a result of Vultron touches on each the human course of and technical work of CVD, we count on that future work will probably be wanted to combine Vultron into higher-level vendor processes, reminiscent of these described within the FIRST PSIRT Companies Framework.
Lastly, we acknowledge that the Vultron protocol effort will finally want to handle syntactic interoperability, reminiscent of message and knowledge trade codecs. We anticipate that this exercise will take some type of engagement with related efforts, such because the Widespread Safety Advisory Framework (CSAF), Open Supply Vulnerability Format, and varied CVE working teams such because the Automation Working Group (AWG).
It isn’t our intent to supplant current format work. Actually, our choice is for Vultron to finally accommodate a wide range of vulnerability knowledge trade codecs. Whereas we admire that incident and malware knowledge trade codecs exist and are associated to vulnerability knowledge trade, we’re primarily serious about vulnerability-specific codecs for now. In case you are conscious of lively vulnerability knowledge trade format efforts that we haven’t talked about right here, please tell us.
[ad_2]