Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
[ad_1]
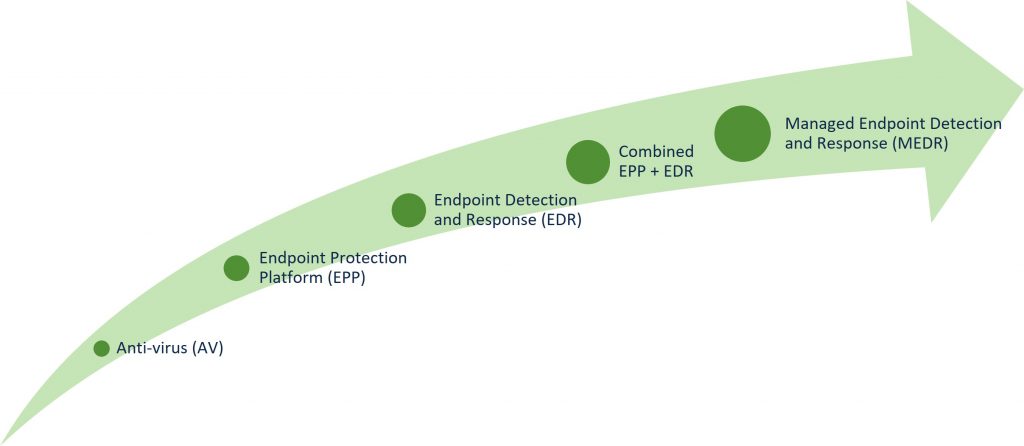
Within the first half of this weblog collection on Unscrambling Cybersecurity Acronyms, we offered a high-level overview of the totally different risk detection and response options and went over how you can discover the suitable resolution in your group. On this weblog, we’ll do a deeper dive on two of those options – Endpoint Detection and Response (EDR) and Managed Endpoint Detection and Response (MEDR). Nonetheless, first let’s have a look again on the historical past of endpoint safety options and perceive how we received EDR and MEDR safety options.
The very first endpoint safety options began out as anti-virus options (AV) with primary safety performance that relied closely on signature-based detection. These options have been efficient towards identified threats the place a signature was created, however ineffective towards unknown threats comparable to new and rising assaults. That meant that organizations struggled to remain forward of attackers, who have been repeatedly evolving their strategies to evade detection with new sorts of malware.
To deal with this drawback, AV distributors added detection applied sciences comparable to heuristics, reputational evaluation, behavioral safety, and even machine studying to their options, which grew to become often known as Endpoint Safety Platforms (EPP). These unified options have been efficient towards each identified and unknown threats and often used a number of approaches to forestall malware and different assaults from infecting endpoints.
As cyberattacks grew more and more subtle although, many within the cybersecurity business acknowledged that safety towards threats wasn’t sufficient. Efficient endpoint safety needed to embody detection and response capabilities to shortly examine and remediate the inevitable safety breach. This led to the creation of EDR safety options, which targeted on post-breach efforts to include and clear up assaults on compromised endpoints.
At present, most endpoint safety distributors mix EPP and EDR options right into a single, converged resolution that gives holistic protection to prospects with safety, detection, and response capabilities. Many distributors are additionally providing EDR as a managed service (often known as MEDR) to prospects who want assist in securing their endpoints or who don’t have the assets to configure and handle their very own EDR resolution. Now that we’ve gone over how endpoint safety advanced into EDR and MEDR safety options, let’s cowl EDR and MEDR in additional depth.
EDR options repeatedly monitor your endpoints for threats, provide you with a warning in case suspicious exercise is detected, and permit you to examine, reply to and include potential assaults. Furthermore, many EDR safety options present risk searching performance that will help you proactively spot threats in your setting. They’re typically coupled with or a part of a broader endpoint safety resolution that additionally consists of prevention capabilities by way of an EPP resolution to guard towards the preliminary incursion.
In consequence, EDR safety options allow you to guard your group from subtle assaults by quickly detecting, containing, and remediating threats in your endpoints earlier than they acquire a foothold in your setting. They offer you deep visibility into your endpoints whereas successfully figuring out each identified and unknown threats. Moreover, you may shortly include assaults that get via your defenses with automated response capabilities and hunt for hidden threats which might be troublesome to detect.
Whereas EDR supplies a number of advantages to prospects, it has some drawbacks. Chief amongst them is that EDR safety options are targeted on monitoring endpoints solely versus monitoring a broader setting. Which means that EDR options don’t detect threats concentrating on different elements of your setting comparable to your community, electronic mail, or cloud infrastructure. As well as, not each group has the safety workers, funds, and/or expertise to deploy and run an EDR resolution. That is the place MEDR options come into play.
Managed EDR or MEDR options are EDR capabilities delivered as a managed service to prospects by third-parties comparable to cybersecurity distributors or Managed Service Suppliers (MSPs). This consists of key EDR performance comparable to monitoring endpoints, detecting superior threats, quickly containing threats, and responding to assaults. These third-parties often have a staff of Safety Operations Middle (SOC) specialists who monitor, detect, and reply to threats throughout your endpoints across the clock by way of a ‘comply with the solar’ strategy to monitoring.
MEDR safety options permit you to offload the work of securing your endpoints to a staff of safety professionals. Many organizations must defend their endpoints from superior threats however don’t essentially have the will, assets, or experience to handle an EDR resolution. As well as, a staff of devoted SOC consultants with superior safety instruments can usually detect and reply to threats sooner than in-house safety groups, all whereas investigating each incident and prioritizing essentially the most crucial threats. This lets you focus in your core enterprise whereas getting always-on safety operations.
Much like EDR although, one draw back to MEDR safety options is that they defend solely your endpoints from superior threats and don’t monitor different elements of your infrastructure. Furthermore, whereas many organizations wish to deploy EDR as a managed service, not everybody needs this. For instance, bigger and/or extra risk-averse organizations who need to make investments closely in cybersecurity are usually happy with operating their very own EDR resolution. Now, let’s focus on how to decide on the suitable endpoint safety resolution when making an attempt to defend your endpoints from threats.
As I discussed in my earlier weblog, there isn’t a single right resolution for each group. This logic applies to EDR and MEDR safety options as effectively since every resolution works effectively for several types of organizations, relying on their wants, assets, motivations, and extra. Nonetheless, one main issue to think about is when you have or are prepared to construct out a SOC in your group. That is essential as a result of organizations that don’t have or aren’t prepared to develop a SOC often gravitate in the direction of MEDR options, which don’t require vital investments in cybersecurity.
One other issue to remember is your safety experience. Even should you’re have or are prepared to construct a SOC, you might not have the suitable cybersecurity expertise and expertise inside your group. Whilst you can all the time construct out your safety staff, you might wish to consider an MEDR resolution as a result of a lack of awareness makes it troublesome to successfully handle an EDR resolution. Lastly, a standard false impression is that you could select between an EDR and a MEDR resolution and that you simply can not run each options. In actuality, many organizations find yourself utilizing each EDR and MEDR since MEDR options typically complement EDR deployments. F
I hope this data and key elements provide help to higher perceive EDR and MEDR options whereas appearing as a information to selecting the right endpoint safety resolution in your group. For extra particulars on the totally different cybersecurity acronyms and how you can determine the suitable resolution in your wants, keep tuned for the following weblog on this collection – Unscrambling Cybersecurity Acronyms: The ABCs of MDR and XDR Safety. Within the meantime, learn the way Cisco Safe Endpoint stops threats with a complete endpoint safety resolution that features each superior EDR and MEDR capabilities powered by an built-in safety platform!
We’d love to listen to what you assume. Ask a Query, Remark Beneath, and Keep Linked with Cisco Safe on social!
Cisco Safe Social Channels
Share:
[ad_2]